Linux configuration files play a crucial role in defining how the operating system behaves and functions. These files form the essential building blocks that contribute to the robust configurability of a Linux system.
This guide delves into the basics of Linux config files, highlighting their importance and pivotal role in the Linux ecosystem.
What Is a Linux Conf File
A configuration (config) file is a handy local file in Linux that influences how a program, utility, or process operates. These files are usually plain text and hold the configurations and guidelines for different utilities, processes and programs.
Config files aren’t meant to be executed; instead, they carry various settings for different aspects of the operating system. These aspects cover processes, user groups, permissions, network access, protocols, and even OS instructions related to reaching internet name servers.
Read: Virtual host configuration in Apache
Importance of Config files
Configuration files are key players in Linux systems. They empower system administrators to personalize the operating system, govern system and application settings, and guarantee that the setup remains intact even after reboots.
Though config files are straightforward, they handle intricate interfaces. A lone config file can dictate numerous system features, playing a vital role in ensuring a well-functioning system.
These files make troubleshooting, backup and version control, easier, maintaining consistency across various systems. They also double up as documentation and hold security policies, adding to their importance in managing and adapting Linux systems.
Types of Config Files in Linux
Configuration files fall into two broad categories:
1. System-wide configuration files: These files impact the entire system and are typically found in the root (/) partition. Modifying them requires superuser access.
2. User-specific configuration files: These files customize the environment based on individual user preferences. They’re usually located in the user’s home directory and don’t need superuser permissions for changes.
Beyond this broad division, Linux configuration files can also be categorized by their type. They play a crucial role in tasks ranging from managing authentication and system administration to fine-tuning the behavior of user programs.
The following sections elaborate on the various types of configuration files in a Linux system and highlight the most significant ones for each category.
Read: Linux directories explained
Network Access Files
The configuration files for network access hold the rules and directions for searching hostnames and managing network access. These files set up and oversee access control policies for both network services and hosts.
Here are the key access files:
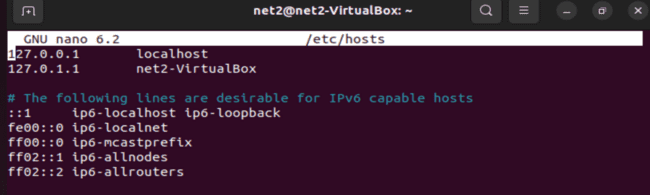
1. /etc/hosts.config: This file holds setup choices for resolving hostnames using the /etc/hosts file.
2. /etc/hosts: This serves as a local database, connecting hostnames to IP addresses, useful when DNS is unavailable or for local network setups.
3. /etc/hosts.allow: It outlines rules permitting network services based on factors like IP addresses or hostnames.
4. /etc/hosts.deny: This file contains rules to block network access to specific services or hosts based on criteria such as IP addresses or hostnames.
In the image below, you can see an example of the /etc/hosts file:
Read: How to Configure Network Settings in Ubuntu 22.04
Booting
The configuration files related to booting impact how the Linux system starts up. These files provide vital system details, handle services that launch at startup, and determine the system runlevels.
Here are the key boot-related files:
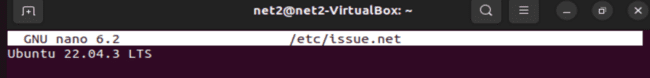
1. /etc/issue: A text file offering system information and a welcome message shown before the login prompt.
2. /etc/issue.net: Similar to /etc/issue but specifically used for network connections and remote logins.
3. /etc/rc.d/rc: This script takes care of managing system runlevels and startup services.
4. /etc/rc.d/rc.sysinit: A script handling essential tasks during system initialization at boot time. This includes hardware setup and mounting filesystems.
5. /etc/rc.d/rcX.d/: This directory holds symbolic links to scripts that control services starting or stopping at different runlevels (X represents the runlevel number).
Read: How to fix Ubuntu boot issues
Login – Logout
The configuration files responsible for login and logout play a crucial role in handling user sessions on a Linux system. They govern how logins work and deliver a friendly message to users as they log in. Here are the key files related to login/logout:
1. /etc/issue: This file gives system details and showcases a welcoming message before the login prompt.
2. /etc/issue.net: It serves the same purpose as /etc/issue but is specifically used for network connections and remote logins.
File System
Configuration files for the file system play a crucial role in managing how storage devices and file systems are accessed and mounted. These files are pivotal in controlling various storage management options. Here are some key file system configuration files:
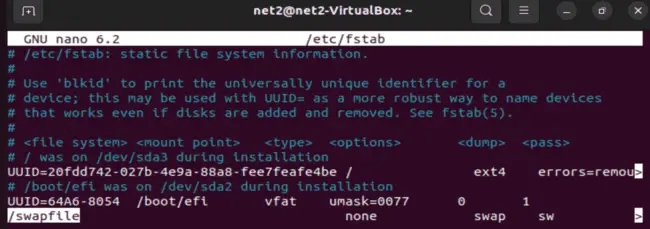
1. /etc/mtab: This file maintains a list of currently mounted file systems, providing details about the device, file system type and mount point.
2. /etc/fstab: Serving as a configuration file, it defines and configures static file system mounts, specifying options for each mount point.
3. /etc/mtools.conf: This configuration file belongs to the mtools package, facilitating access and management of MS-DOS (FAT) file systems. It specifies settings for tools like mdir and mcopy .
In the image below, observe the /etc/fstab file featuring a line ensuring the persistence of the swap partition across reboots:
Read: How to list, start and stop services at boot time in Linux Ubuntu/Debian
System Administration
Some files in Linux are very important for managing the system and keeping it safe. These files have information about users, groups, files, and security rules. We call these files system administration configuration files.
Some of these files are:
1 /etc/group. This file has information about groups of users, like their names and which users belong to them.
2 /etc/nologin. This file stops some users from logging in, usually when the system needs to be fixed or updated.
3 /etc/passwd. This file has information about user accounts, like their names, IDs, home folders, and shells.
4 /etc/rpmrc. This file has information about RPM, which is a tool for installing and removing software on the system.
5 /etc/securetty. This file has information about terminals, which are devices that let users interact with the system. This file only allows the root user, who has the most power, to log in from certain terminals.
6 /etc/usertty. This file has information about which terminals each user account can use. 7 /etc/shadow. This file has information about passwords and security for user accounts. This file makes passwords more secure by hiding them.
Read: 12 Linux Basic Health Check Commands for Monitoring Performance
System Commands
Some files in Linux have information about system tools and commands that are used for running and managing the system. These files help to set up and control system tools and commands, so that the system can work well and do what it needs to do.
Some of these files are:
1 /etc/lilo.conf. This file has information about LILO, which is a tool that helps the system to start and choose between different operating systems.
2 /etc/logrotate.conf. Has information about logrotate, which is a tool that helps to manage log files and decide when and how to change them.
3 /etc/identd.conf. Contains information about Ident, which is a tool that helps to find out who owns TCP connections and which is used for network services like IRC.
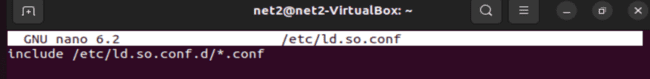
4 /etc/ld.so.conf. This is about where the system should look for shared libraries that are needed for running executable files.
5 /etc/inittab. It has information about init, which is a tool that helps to set up the system and decide what to do when the system starts.
6 /etc/termcap. Contains information about terminals, which are devices that let users talk to the system. This file helps applications to work with terminals correctly.
The image below shows an example of the /etc/ld.so.conf file, revealing the directories the system searches for dynamic links to executable files.
Read: What to do when Ubuntu freezes
Daemons
Daemons are important processes that run in the background and do certain tasks when the system, network, or hardware asks them to. Configuration files for daemons help to set up how they work and what they do.
Some of these files are:
1 /etc/syslogd.conf. This file has information about the syslog daemon (syslogd), which helps to manage system and application logs, deciding what to do with log messages and where to keep them.
2 /etc/httpd.conf. This file has information about the Apache HTTP server (httpd), which helps to serve web content, defining server settings, virtual hosts, and how to act.
Networking
Some files in Linux have information about network-related settings, services, and protocols that are used for running and managing the network. These files help to set up and control how the network works and connects.
Routing files
These files are related to the routing of network traffic, which is the process of deciding how to send packets from one network to another.
- /etc/gated.conf. This file tells the gated routing protocol daemon, which is a tool that helps to decide how to route network traffic, what to do.
- /etc/gated.version. This file shows the version number of the gated daemon.
- /etc/gateway. This file is an optional file that tells the routed daemon, which is another tool that helps to route network traffic, what to do.
Network configuration files
These files are related to the configuration of network interfaces, which are the devices that connect to the network, such as Ethernet cards or wireless adapters.
- /etc/networks. This file lists the names and addresses of networks that your network can reach. This file is used by the route command, which is a tool that helps to set up network routing.
- /etc/sysconfig/network. This file tells whether networking is enabled or not. This file is read when the system starts.
- /etc/sysconfig/network-scripts/if*. These files tell Red Hat network configuration scripts, which are tools that help to manage network interfaces, such as eth0 and wlan0, what to do.
Network protocol files
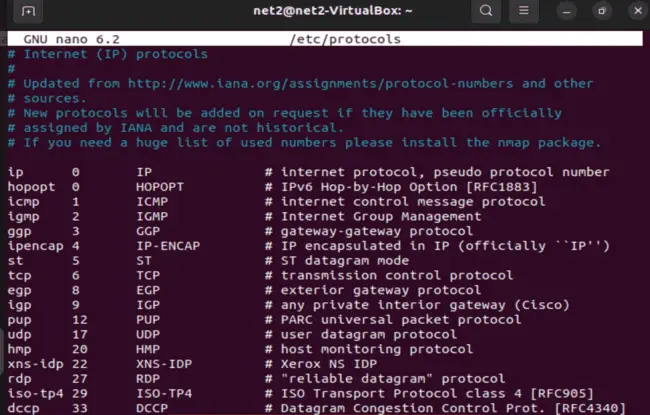
These files are related to the network protocols, which are the rules and standards that govern how network communication works, such as TCP and UDP.
- /etc/protocols. This file lists the network protocols that are available for network communication, such as TCP and UDP.
- /etc/resolv.conf. This file tells which name server to ask when looking for IP addresses, such as www.bing.com.
- /etc/rpc. This file gives the rules for Remote Procedure Call (RPC), which is a tool that helps to do things on remote systems, such as NFS, which is a tool that helps to share files between systems.
Network service files
These files are related to the network services, which are the programs that provide or use network functionality, such as HTTP and FTP.
- /etc/exports. This file tells how to export file systems via NFS, including who can access them and what they can do.
- /etc/services. This file tells the names, port numbers, and protocols of network services, such as HTTP and FTP, which are used by various network-related programs.
- /etc/inetd.conf. This file tells inetd, which is a tool that helps to control daemons or services for various network services, such as telnet and ftp, what to do.
- /etc/sendmail.cf. This file tells sendmail, which is a tool that helps to send and receive emails, what to do.
Here is a sample output of the /etc/protocols file :
User Programs
Sure, I can try to reword the text below using simple English and human-like language. Here is one possible way to do that:
You can change how user programs work by using configuration files. These files are not easy to see and they are kept in your home folder. They start with a . (dot), like .config or .appname. You can see them with the ls command.
When you start user or system programs, they look at their configuration files. They first read the config files in the /etc/ folder. Then, you can change them with the rc and . (dot) files.
If you like the content, we would appreciate your support by buying us a coffee. Thank you so much for your visit and support.