Spy applications, called spyware or stalkerwares are usually installed on a person’s cell phone without his/her knowledge in order to track all of his/her activities. Criminals can access the device’s location history, SMS messages and social media conversations and even audio and video recorded with the phone’s microphone and camera, without the user noticing it. In addition to being used by crooks, these apps are also commonly used by controlling relatives and jealous partners.
Read more : A well researched article on anti-spyware apps from Anjelica Rivera at celltrackingapps.com
In this article, we will first provide some helpful information on how to be vigilant, what to avoid and what anti spyware apps can be used to prevent others from spying on you.
How to find out if your smartphone is being monitored ?
Slow access to some applications and increased battery or data consumption may be indications that the smartphone is being monitored. Here are some tips that help determine if someone is spying on your smartphone:
- Periodically review the applications installed on your smartphone as well as which ones are allowed to access the microphone, camera and location services. If you identify a suspicious program, uninstall it immediately.
- Many spy apps are real data hogs because they not only monitor the device, but also transmit personal information. If your data usage skyrockets, check the apps installed.
- The Web WhatsApp can also be a simple way to spy . To avoid misuse, access WhatsApp Web through the app and end all active sessions. Facebook, Instagram and Twitter offer a history of access to their programs and thus it is possible to identify unauthorized access to the account.
Read: How Can Someone Clone Your Cell Phone To See Text Messages And Other Data Remotely
- If there is a suspicion that the phone is being spied on, the fastest way to solve the problem is to restore the device to factory settings . First, back up personal files (photos, videos and documents) to a cloud service in order not to lose any records. If your device is infected, it is also advisable to change the passwords for all accounts and services used from the smartphone. Users should also delete devices linked to messenger apps, e.g. for browser use, in the messenger settings.
- Protect your devices with secure passwords and never reveal them, even to your relatives or partners.
- Do not leave your phone unlocked anywhere without supervision. Most stalkerwares require physical access to the device to perform the installation.
- Disable fingerprint unlocking. Controlling and jealous partners can press your finger against the reader while you sleep.
- Block the installation of applications from external sources.
- Keep your device’s antivirus up to date.
Is it possible to spy on cell phones with only the number?
Spy apps are installed through physical access to the cell phone , as activation permissions must be accepted in the app itself. Therefore, it is not possible for someone to be able to infect a device just through the cell phone number or via Bluetooth, for example.
Read: How to copy paste between Windows 10 and Android
However, the malware can be installed through phishing scams with corrupted links or messages that, in addition to allowing the installation of the spy app, are already capable of stealing personal information. The malware can also come with downloads made illegally on unofficial platforms.
Spy apps affect only the smartphone?
A spyware is not able to infect cell phone chips – so the cell phone number cannot be used by the hacker as mentioned previously. However, all information saved on the smartphone, such as bank passwords, text messages and Internet search history , are in danger, as the spy can have access to any and all types of information stored in the smartphone, which include photo gallery, installed apps and even access to the phone’s camera and microphone.
Read: Best android messaging apps
Is the spy app undetectable?
Spy applications can be detected by some antivirus apps . In addition, the smartphone may show some signs that it has been infected by malware . Cell phone batteries running out quickly and suddenly, mobile data with high usage spikes throughout the day or suspicious notifications appearing frequently can be signs that the cell phone has been infected and hackers may be spying on your actions.

Are spy apps dangerous?
Spyware and stalkerware can access personal information, including bank passwords and access to social networks , for example. In addition, the hacker has access to the victim’s location through the cell phone’s GPS, can intercept calls and messages and is able to monitor all of his digital steps. It may also be possible to lock and unlock the device remotely and delete information, while also having access to the smartphone’s camera and microphone.
Read: How Does a GPS Work and Which Industries Benefit From It
Get out of the sight of the curious
Make sure to set a complex password to protect your device. If your device supports alphanumeric passwords, use them, but leave no trace. If the code is a 4-digit number, avoid important dates such as your birthday or your wedding dates.
Now, if you choose a password based on gestures that form drawings to unlock the device, make a more complex drawing and wipe the screen of the phone every time you swipe to unlock it. A more attentive onlooker can check the trail left by skin fat on the device screen and memorize the design that unlocks the device.
Bluetooth and Wi-Fi
If you prefer not to install anything (it may be that your problem with privacy invaders is not that serious), there are simple tips that will make your life easier and make it more difficult for eavesdroppers. One is to disable Bluetooth and Wi-Fi whenever you are in a public place or are not using these functions. The wireless connection can open doors for attackers.
Read: How to fix bluetooth problems in Windows 10
Whenever possible, prefer to use the 3G or 4G network when you are away from home, especially if you are going to use bank applications or carry out bank transactions in the browser as public wireless connections can be fragile in terms of security, especially when they do not have a password. While it is possible for thieves to break into the mobile network, it will not be as easy as on Wi-Fi.
Anti Spy Mobile Free
The Anti Spy Mobile application is an excellent tool to analyze your phone and check if it is being tapped by third-party malicious software.

According to its developers, this free tool is able to analyze your phone immediately, warning you if there are hidden spy apps installed on your Android. There is also the possibility of automatically removing malicious applications, however, you will have to purchase the PRO version.
FREE Spyware Removal
FREE Spyware Removal is another anti-spy application . It is a recent tool that aims to examine your smartphone and check if there is a spy app installed on your Android. It may seem unlikely, but to eliminate all doubts and maintain your security and privacy, it is worth checking out this free application. You never know if your wife, husband, employer, partner, stranger, stalker or someone close to you, apparently unsuspecting, has any interest in spying on you.
The developers claim that this is a great solution for detecting commercial spy apps that are easily accessible, which can be purchased by anyone with a credit card and the internet.
Read: IPhone privacy settings you should activate
Anti Spy Mobile
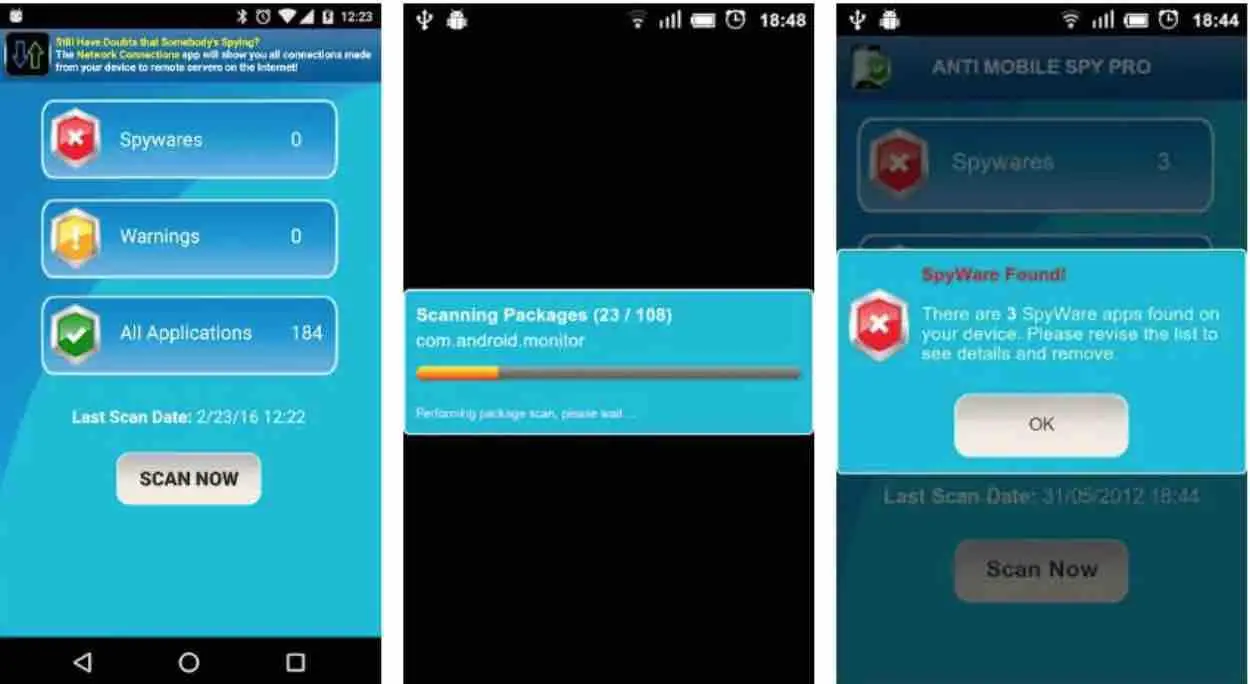
It acts as a software scanner to identify possible harmful threats to your mobile phone. In addition, it not only analyzes the applications that you already have installed, but also websites or online downloads.
Incognito Spyware detector
It is an app that tries to protect the device from applications with built-in viruses. It detects those tools that threaten the smartphone in a hidden way, since they are marketed as programs with parental control. 
Camera Block Free

There are many theories on the internet that mobile cameras are the preferred tools of hackers to spy and extort many users. In fact, many cases have already been counted. This app completely blocks both the front and rear cameras , preventing them from being activated.
Read: How to Protect Your Site from Malware
Malwarebytes protection
Most users install it to act as an antivirus, but the truth is that it also works to detect spy threats. Applications that track locations, voice and calls, none will resist this program, as well as links that can be sent through social networks.
Camera and microphone blocker
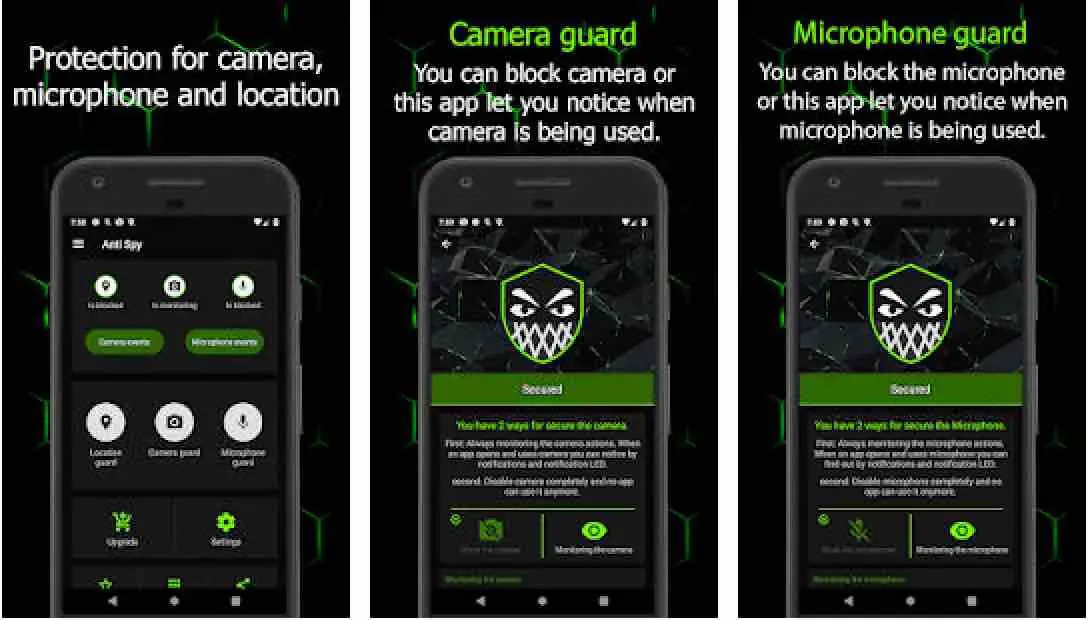
This app goes a bit further, since in addition to blocking the camera, it also disables the microphone. Sadly, it is another of the most recurrent means of spying and capturing conversations, so it can be a very useful program to avoid falling into these uncomfortable situations. In fact, it notifies when both sensors are activated or not and slso creates a fake location to ‘mislead’ hackers.
SpyWare Removal (Anti Spy)
Apart from scanning espionage threats and being able to create a list of exceptions, this anti spy app has a more pedagogical section, since it shows basic tips to avoid being intimidated virtually. Moreover, it shows the details of each application such as the location, the microphone or the camera. More specifically, it shows the permissions that each app has.

Anti Spy and Spyware Scanner
It uses artificial intelligence to incisively identify as hidden ads, fake apps, fraudulent SMS or spam. The app can do automatic scans, but if you prefer, you can do it manually to have greater security, every time you download a new app or update an already installed one.

If you like the content, we would appreciate your support by buying us a coffee. Thank you so much for your visit and support.

